What Is Meant by Cloud Security?
Cloud security is similar to traditional IT security, but focuses on policies and controls employed to protect data, software applications, and associated cloud computing infrastructure.
Cloud computing dates back to the 1960s. Today’s widespread adoption of cloud services in business and personal life has driven the need for robust secure practices and controls.
What Is a Cloud Security Model?
Cloud computing comes in several deployment options (called models), including public, private, and hybrid cloud. In the chart below, you can find the specific cloud management information associated with each deployment model:
| Deployment Model | Description | Target Users | Use Case | Benefits |
|---|---|---|---|---|
| Public Cloud | Third-party cloud service providers (like Microsoft, Amazon, and Google, the three most popular) own these resources (i.e., hardware, software, and infrastructure). Companies share these resources with other organizations. | Software developers and testers | Commonly used for email, office applications, and storage |
|
| Private Cloud | A single business owns these resources, which a third-party service provider or the organization’s data center can host. | Government and financial institutions | Commonly used for sensitive workloads in highly regulated industries |
|
| Hybrid Cloud | This deployment model distributes workloads across public and private cloud infrastructure. Applications share resources and are interoperable between the public and private cloud, based on security and performance needs. | Entities that serve multiple organizations with differing regulations and security requirements | Commonly used by startups that have inconsistent and unknown requirements and IT service providers with a variety of customers |
|
For those who are using different clouds for different tasks, multi-cloud models are also available. Unlike the hybrid cloud, multi-cloud solutions serve organizations that use a variety of different public cloud services from different providers. An organization may also have a private cloud infrastructure and even an on-premises infrastructure. You use each of these environments for their own independent, siloed purpose. The hybrid cloud, on the other hand, always includes public cloud and private cloud infrastructure that work together and intermingle.
Individuals or organizations from specific business sectors that have similar concerns when it comes to privacy, security, and compliance share what’s known as a community cloud. Such organizations include banks, hospitals, and government agencies.
The Difference Between Cloud Security and Traditional IT Security
Traditional IT and cloud technology face the same exposure to data theft, leaks, and disruptions. The main difference between the two technologies is that cloud computing resources are more abstract than traditional on-premises hardware, servers, and software.
Traditional IT infrastructure encompasses the in-house purchasing, installation, and management of dedicated hardware, software, and other infrastructure items. With traditional IT infrastructure, you have full local control of your company’s data, applications, and infrastructure, creating a seemingly secure system. As your organization grows and data storage requirements increase, you will purchase additional hardware to meet your capacity needs. Traditional IT environments allow a connection between hardware devices and the servers located in your on-premises data center and rely on perimeter security models.
Cloud computing is abstract when compared with traditional IT infrastructure. Cloud computing resources are not physically accessible or on premises. The cloud offers a virtual solution, allowing companies to achieve external hosting by renting server space from a cloud service provider. This arrangement puts the cloud service provider in charge of security. You access cloud computing environments by using application programming interfaces (APIs). APIs enable communication between your devices and the cloud servers. The cloud environment is only as secure as these APIs. Although traditional and cloud security rely on similar methods, increasingly complex cloud infrastructure and increasingly sophisticated security threats are forcing a transition away from perimeter security and toward cloud computing that uses stronger authentication and encryption methods.
The contrasts between cloud and traditional may make cloud computing seem unreasonably insecure, but with proper precautions and the right cloud service provider, the benefits of cloud computing outweigh the risks, making cloud security a no-brainer for most organizations.
How Secure Is the Cloud?
Cloud services have become very common, but security concerns remain top of mind. Maintaining security, availability, and privacy is crucial for businesses. Cloud data centers are usually staffed by cloud security experts, audited by third-party organizations, and held to strict policies and standards. Many of these centers are Health Insurance Portability and Accountability (HIPAA) and Peripheral Component Interconnect (PCI) compliant and follow Statements on Standards for Attestation Engagements (SSAEs). These cloud service providers have committed to robust security requirements and proven their ability to protect sensitive information.
Why Is Cloud Security So Important?
With spending for cloud computing continuing to increase, cloud security is more important than ever. According to RightScale’s State of the Cloud Survey, 96 percent of IT professionals are using the cloud. Enterprise public cloud spending is expected to grow quickly and significantly.
Cloud service providers are a target for hackers. Below are the top cloud security threats facing these providers, according to the Cloud Security Alliance® (CSA):
- Data breaches
- Insufficient identity, credential, and access management
- Insecure interfaces and APIs
- System vulnerabilities
- Account hijacking
- Malicious insiders
- Advanced persistent threats (APTs)
- Data losses
- Inadequate due diligence
- Abuses and nefarious uses of cloud services
- Denial-of-service attacks (DDoS)
- Shared technology issues
Other security threats include the following:
- Ransomware, such as BadRabbit
- Coin mining
- Cryptojacking
- Trojans, such as Dridex, Trickybot, Zbot, and Emotet
- Windows security issues, such as EternalBlue
- Grayware
- Hackers “living off the land”
- Malware, such as Petya/NotPetya, which takes advantage of software updates, and which takes advantage of CPU flaws and the breakdown of security measures, such as Meltdown, Spectre, and single-point-of-failure issues
- Worms, such as Ramnit
- Spear phishing
- Unpatched software vulnerabilities (known as Zero Days)
- Social engineering attacks
- Network eavesdropping
- Human error
- Stolen credentials
- Abuse by employees
- Negligence
- Unauthorized use
- Undeleted data
- Loss of data that occurs when a cloud service provider goes out of business
- Unskilled or overworked IT staff
- Shadow IT
Benefits of Cloud Security
Following cloud security best practices and implementing adequate preventative measures can provide peace of mind that your data and systems are safe, ensure visibility into security measures, allow you to deliver alerts, and prepare you for when unusual activities occur. Committing to these practices can also help you ensure that you’ll have the availability, reliability, and security to operate without disruption.
Cloud Security Provider Responsibilities
With the rapid demand for cloud computing services, service providers are popping up everywhere, offering a wide variety of amenities, including layers of cloud, infrastructure as a service (IaaS), platform as a service (PaaS), software as a service (SaaS), cloud storage, testing, integration, and cloud-native applications. The most popular cloud services come from household names such as Amazon, Microsoft, Google, and IBM.
The growing demand for cloud computing services is increasing the demand for cloud security. Most cloud service providers have very strict regulatory standards, accessible security tools, practices to maintain data confidentiality, and protection against DDoS attacks. When evaluating cloud service providers, be sure to ask each provider about the following security measures:
- Identity management
- Physical security
- Training for personnel
- Privacy, confidentiality, data integrity, and access control
- Business continuity and disaster recovery
- Encryption method, e.g., attribute based (ABE), ciphertext policy-ABE (CP-ABE), key policy-ABE (KP-ABE), fully homomorphic (FHE), or searchable encryption (SE)
- Logs and audit trails
- Unique compliance requirements, such as HIPA
Security Challenges That Come with Providing Cloud Solutions
As mentioned earlier, hackers, malware, and ransomware are threats that come with cloud computing. Along with common cloud security issues come legal and liability challenges.
- The influx of information stored by cloud service providers makes them prime targets of malicious activity.
- Cloud solution providers are responsible for intellectual property and terms surrounding data loss or compromised data.
- Requirements to retain or even provide public records upon request can put cloud service providers in an uncomfortable position.
- The number of cloud implementations can easily get out of hand, as requirements for data and information storage may limit decommissioning opportunities.
The ease of access to and vast availability of cloud solutions challenge businesses and organizations as well. Employees can easily take advantage of cloud solutions and apps, causing internal IT departments to lose control over IT services. Shadow IT leaves an organization at risk — the organization is in the dark regarding the services being utilized, the location of information, the people who have access, and security policies. These factors make it difficult to enforce security policies, leaving a business at risk of non-compliance with regulatory mandates.
Cloud Solution Security Architecture
The number one goal of all established cloud service and solution providers is to keep proprietary and confidential data secure. Providers design and build solutions based on the requirements and protocols to secure your data and the need to offer flexibility. Both the cloud service/solution provider and the customer are responsible for security. Provider service-level agreements should indicate the customer’s level of responsibility. The cloud service provider will have developed a cloud security architecture that demonstrates how their cloud is secured.
What Are Cloud Security Standards?
Cloud security standards are security-related standards, controls, and specific guidance that various industry organizations, including the International Organization for Standardization (ISO), the CSA, and others, outline and define for cloud service providers and cloud service customers.
Cloud Security Controls and Standards
The CSA is dedicated to defining and raising awareness of cloud computing best practices. In addition to defining the top security threats mentioned above, they have designed the Cloud Security Alliance Cloud Controls Matrix (CCM) to provide guidance across governance and operations domains. These domains include the following:
- Application and interface security
- Audit assurance and compliance
- Business continuity management and op resilience
- Change control and configuration management
- Data security and information lifecycle management
- Datacenter security
- Encryption and key management
- Governance and risk management
- Human resources security
- Identity and access management
- Infrastructure and virtualization
- Interoperability and portability
- Mobile security
- Security incident management, e-disk, and cloud forensics
- Supply chain management, transparency, and accountability
- Thread and vulnerability management
The CCM provides a framework of 133 controls that are aligned with the 16 domains and focuses on deterring, preventing, detecting, and correcting security issues.
In addition to the CSA, the National Institute of Standards and Technology (NIST) is a non-regulatory agency established by the U.S. Commerce Department to develop industry standards that encourage innovation. NIST cloud computing guidelines are published under the special publication (SP) 800 series and apply to federal agencies.
NIST provides a report (NIST SP 500-322) that helps qualify a cloud service as aligned with the NIST definition of cloud computing (NIST SP 800-145). This report provides guidance to analyze the essential characteristics of cloud computing, cloud service models, and cloud deployment models.
Cloud Security Best Practices
Cloud computing offers organizations many benefits, but companies need to implement protective measures to defend themselves from threats. In addition to implementing the CSA and NIST best practices, organizations can institute additional security controls such as the following:
- Use only known and trusted software.
- Understand compliance regulations.
- Manage the lifecycle of cloud instances, applying patches and upgrades.
- Continuously monitor for cloud security breaches.
- Choose skilled cloud providers — evaluate them against strict requirements.
- Ensure you can port your workload to another provider if necessary.
- Deploy additional security measures (in addition to what the cloud service provider offers) to protect yourself from compromised cloud infrastructure.
- Use cloud access security broker (CASB) software and perform cloud vulnerability testing using scanning and penetration testing products.
- Put together a cloud incident response plan.
- Replace any legacy security solutions, including computer and network security.
- Consider DevOps and DevSecOps to integrate security into the development team’s projects.
- Unify and centralize security practices across all cloud services.
- Maintain a complete list of all cloud assets.
- Understand cloud security best practices.
- Train employees on cloud security.
- Follow security best practices.
- Automate to remove human error.
- Secure APIs properly.
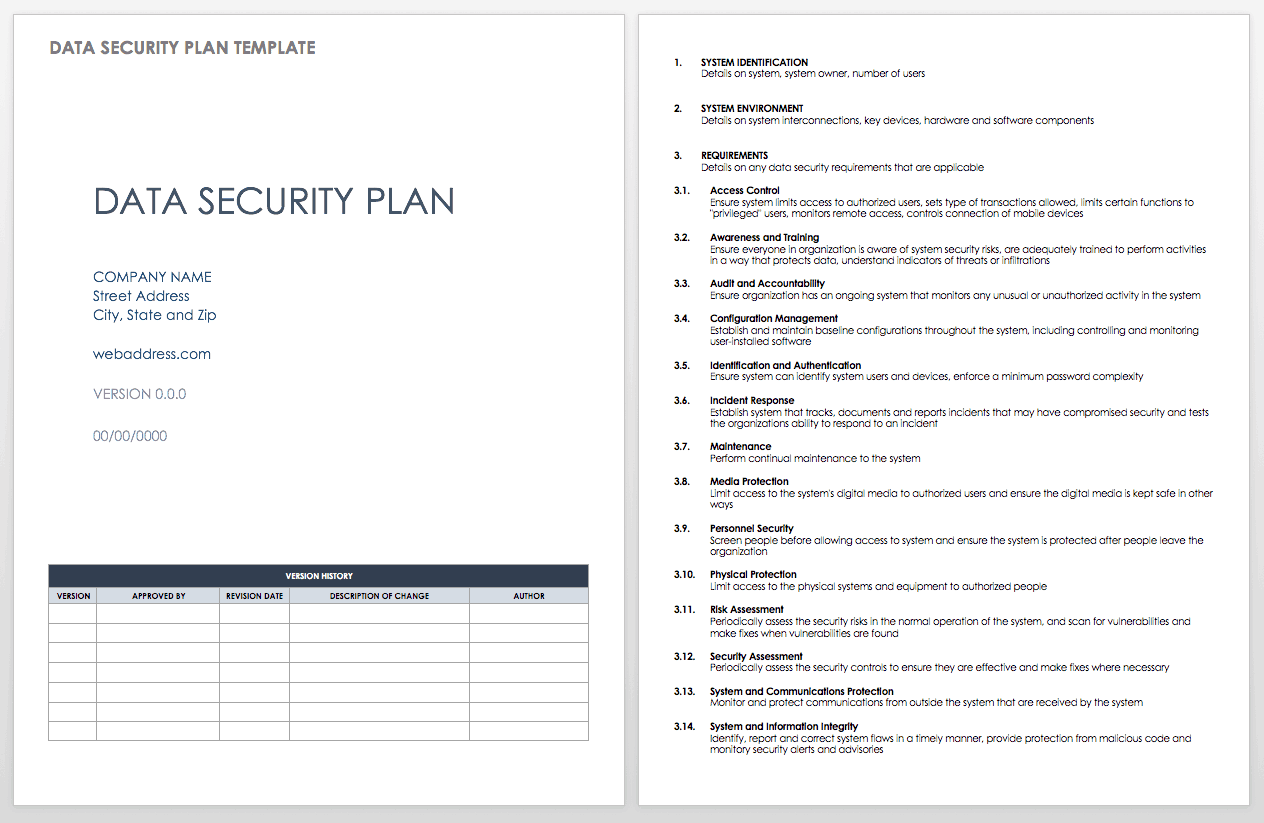
When establishing cloud security standards, you can create a data security plan for your organization. This customizable template provides guidance on how to handle data on the premises and in the cloud.
Download Data Security Plan Template
What Is the Cloud?
Simply put, the cloud is the internet. The cloud makes resources, software programs, information, and services available over the internet rather than on your local computer. These resources are stored on physical servers somewhere in a data center, but the cloud removes the need for on-premises hardware infrastructure. Below is a comparison of cloud technology with traditional technology
| Cloud | Traditional |
|---|---|
| Applications and data are stored in third-party data centers (reducing administration). | Applications and data are stored on local computers or in in-house data centers. |
| Minimal infrastructure investment | High infrastructure investment |
| Easy and fast to scale | Slow to scale |
| Usage-based fees (which may be more cost effective) | Fees regardless of usage |
How Does the Cloud Work?
The cloud works by allowing users to access data and applications over the internet, regardless of their location and device.
Are Public Clouds Secure?
Public clouds are secure if the service provider is secure. You can evaluate a cloud provider’s security by looking at their compliance audits, asking them questions based on the best practices outlined above, and touring their facilities.
The Future of Cloud Security
For many organizations, cloud services have gone from a luxury to a strategic priority. The extensive amount of data stored in the cloud makes it an enormous target for hackers, fraudsters, and cybercriminals. The colossal ramifications of these potential threats have made security a top industry priority. We are already experiencing more robust authentication methods in the forms of multi-factor and biometric authentication.
Improve Information and Data Security with Smartsheet
Empower your people to go above and beyond with a flexible platform designed to match the needs of your team — and adapt as those needs change.
The Smartsheet platform makes it easy to plan, capture, manage, and report on work from anywhere, helping your team be more effective and get more done. Report on key metrics and get real-time visibility into work as it happens with roll-up reports, dashboards, and automated workflows built to keep your team connected and informed.
When teams have clarity into the work getting done, there’s no telling how much more they can accomplish in the same amount of time. Try Smartsheet for free, today.
Any articles, templates, or information provided by Smartsheet on the website are for reference only. While we strive to keep the information up to date and correct, we make no representations or warranties of any kind, express or implied, about the completeness, accuracy, reliability, suitability, or availability with respect to the website or the information, articles, templates, or related graphics contained on the website. Any reliance you place on such information is therefore strictly at your own risk.
These templates are provided as samples only. These templates are in no way meant as legal or compliance advice. Users of these templates must determine what information is necessary and needed to accomplish their objectives.