Remote Access Workers on the Rise
According to research conducted by Gallup, 43 percent of workers in the U.S. worked remotely at least some of the time in 2016. Remote workers report higher job satisfaction and flexibility, experience fewer distractions and interruptions, and are more productive. Companies experience less absenteeism, less stress on office accommodations, and realize greater employee retention. A recent New York Times article found that finance, insurance, real estate, and transportation were most likely to have and support remote work (retail and education were least likely candidates). The trend is only increasing: the 2016 Gallup poll also found that those who work remotely log more hours away from the office than was reported in their 2012 findings. Not only are people logging more hours, but remote workers are saving money when it comes to commuting costs and businesses are saving on office space expenses.
While remote work is not available to or appropriate for everyone, non-self-employed work at home opportunities have grown by 115 percent since 2005 - especially for non-union, college educated, and high wage workers, according to Global Workplace Analytics.
What Is Remote Access?
Remote access is any connection made to an organization's internal network and systems from an external source by a device or host. Remote locations can be almost anywhere in the world, from the employee’s home to an off-site office, hotels, transportation hubs, and cafes.
What Is a Remote Access (Control) Policy?
Increased availability and usability of mobile devices and remote accessibility services allow for greater worker flexibility whether they work from home, on the road, or at a remote office space. However, access from outside the physical walls and firewall protections of the company can invite numerous connectivity, confidentiality, and information security challenges. The hazards to sensitive or proprietary information through unauthorized or inappropriate use can lead to compliance problems, from statutes such as those found in the Health Insurance Portability and Accountability Act (HIPAA) or Payment Card Industry Data Security Standards (PCI DSS). Loss can also take the form of industrial espionage, theft, or accidental disclosure of intellectual property, or damage to public image or industry standing. There are numerous stories of devices loaded with confidential information being hacked or physically stolen from cars or left in hotels or restaurants. Additionally, there are recent stories of people hacking high-level officials who have inadequate passwords and then subsequently leaking embarrassing information. These types of incidents are more likely to occur without enforcement of internal and external Network Security Policies (NSP).
The Information Technology (IT) department within an organization is generally responsible for creating, governing, and enforcing an NSP. A remote access policy statement, sometimes called a remote access control policy, is becoming an increasingly important element of an overall NSP and is a separate document that partners each and every remote user with the goals of an IT department. The document defines the rules for proper use, guidelines, and practices, as well as the enforcement mechanisms for compliance. You’ll find remote access policies implemented across every industry vertical, including healthcare, government, manufacturing, and finance, and they apply to all remote workers across all departments
What Is a Network Security Policy?
A remote access policy is commonly found as a subsection of a more broad network security policy (NSP). The network security policy provides the rules and policies for access to a business’s network. It commonly contains a basic overview of the company’s network architecture, includes directives on acceptable and unacceptable use, and outlines how the business will react when unacceptable or unauthorized use occurs.
Why Is a Remote Access Policy Necessary?
The numerous types of mobile devices and the different ways to connect pose challenges for the IT department. Devices can include cell phones, tablets, laptops, and any other device a remote worker relies on to conduct business. They can be company owned and secured, personally owned and authorized by a Bring Your Own Device (BYOD) policy, or a combination. Each class of device has its own set of security challenges. According to the National Institute for Standards and Technology’s Guidelines for Managing the Security of Mobile Devices in the Enterprise, “…Security controls available for laptops today are quite different than those available for smartphones, tablets, and other mobile device types.” Since different devices demand different controls, the policy has to detail what is allowed, compliant, and secure. The policy should answer the following questions:
- Does the remote device have the latest anti-malware and operating systems?
- Is it being used for personal business?
- Is it connected to a Local Area Network (LAN), Virtual Private Network (VPN), or other service?
- Can the employee store sensitive information on the device, and is it adequately protected?
In addition, be sure to outline issues such as passwords and authorized sites or emails to provide network protection and security.
Address each connectivity element separately. For example, remote access might involve a VPN, logging into a cloud-based technology (such as a customer database or Dropbox), accessing web-based email, or using Windows Remote Desktop. Some companies do not allow access from personal machines, while others enforce strict policies for BYOD situations - many predict a rise in BYOD. In fact, in the article My Vision for the Future, part of Virgin’s Future Visions series, the authors state that within the next 20 years, “Businesses will see an erosion of centralized computing by the idea of BYOD [Bring Your Own Device].” Policies will have to continually adapt to account for rapidly changing technologies, connectivity that increasingly depends on cloud and wireless systems, and a workforce that continues to demand more flexibility in order to enjoy enhanced work-life balance.
Benefits of a Remote Access Policy
There are numerous benefits to having and enforcing a remote access policy. Software organizations where development engineers need to connect across multiple locations, small organizations lacking office-space, and large, enterprise organizations all want to offer the most flexible work options in order to attract high-ranking candidates and reap the rewards of having such a policy.
There are two overarching goals for remote access that must work simultaneously: to provide appropriate access that allows remote workers to be productive, and to protect the information assets and systems from accidental or malicious loss or damage. In an era of increasing compliance statutes that protect privacy and identity, strong network and remote policies provide guidelines to prevent data misuse or mishandling. Policies also offer guidance to the remote user and set expectations that identify issues such as anti-malware and operational system requirements, firewalls, and password protection.
Policies for VPN remote access can be standardized. These policies “shore up” and prevent the use of rogue devices and access by non-authorized users, including the worker's family members or housemates. The policy also enforces proper email protocols to protect information from being sent through unsecured or untrusted sources, and also provides rules that limit or prohibit split tunnel configurations that allow mobile users to access both secure and unsecure networks simultaneously.
Challenges of Remote Access
There are plenty of advantages to remote access, but there are also instances where remote access is simply not feasible. For example:
- Organizations with strict, government access restrictions due to sensitive information.
- Retail and food-service workers.
- Workers who lack discipline outside of the office.
- Organizations that lack the infrastructure to provide security appliances and technology.
- Employees who are necessary to complete an assembly line production process.
- Medical record staff.
What Should Be Included in a Remote Access Policy?
Policies for using company systems involve security, confidentiality, the integrity of information, and a hierarchy of access or availability. Remote policies have guidelines for access that can include the following:
- Hardware and software configuration standards for remote access, including anti-malware, firewalls, and antivirus
- Encryption policies
- Information security, confidentiality, and email policies
- Physical and virtual device security
- Access privileges, authentication, and access hierarchy
- Connectivity guidelines
- Password protocols
- Acceptable use policies
- Third-party protections and standards (trusted vs. non-trusted sources or hosts)
- Policy compliance, governance, and enforcement
- Access and equipment ownership requirements
The policies can also be customized to determine the time of use, time-out policies for disconnecting when idle, and determinations for where connectivity is prohibited (such as coffee shops or malls). The policies can also specify which hosting, software, antivirus, or hardware to use.
Problems associated with unauthorized access by hackers or even family members can be clearly defined and enforced. Even if the employee provides their own equipment, laptop, or mobile device, the policy dictates and enforces the minimum-security requirements necessary. The policy can also provide determinations on who is allowed remote access, the level of access, and penalties for misuse.
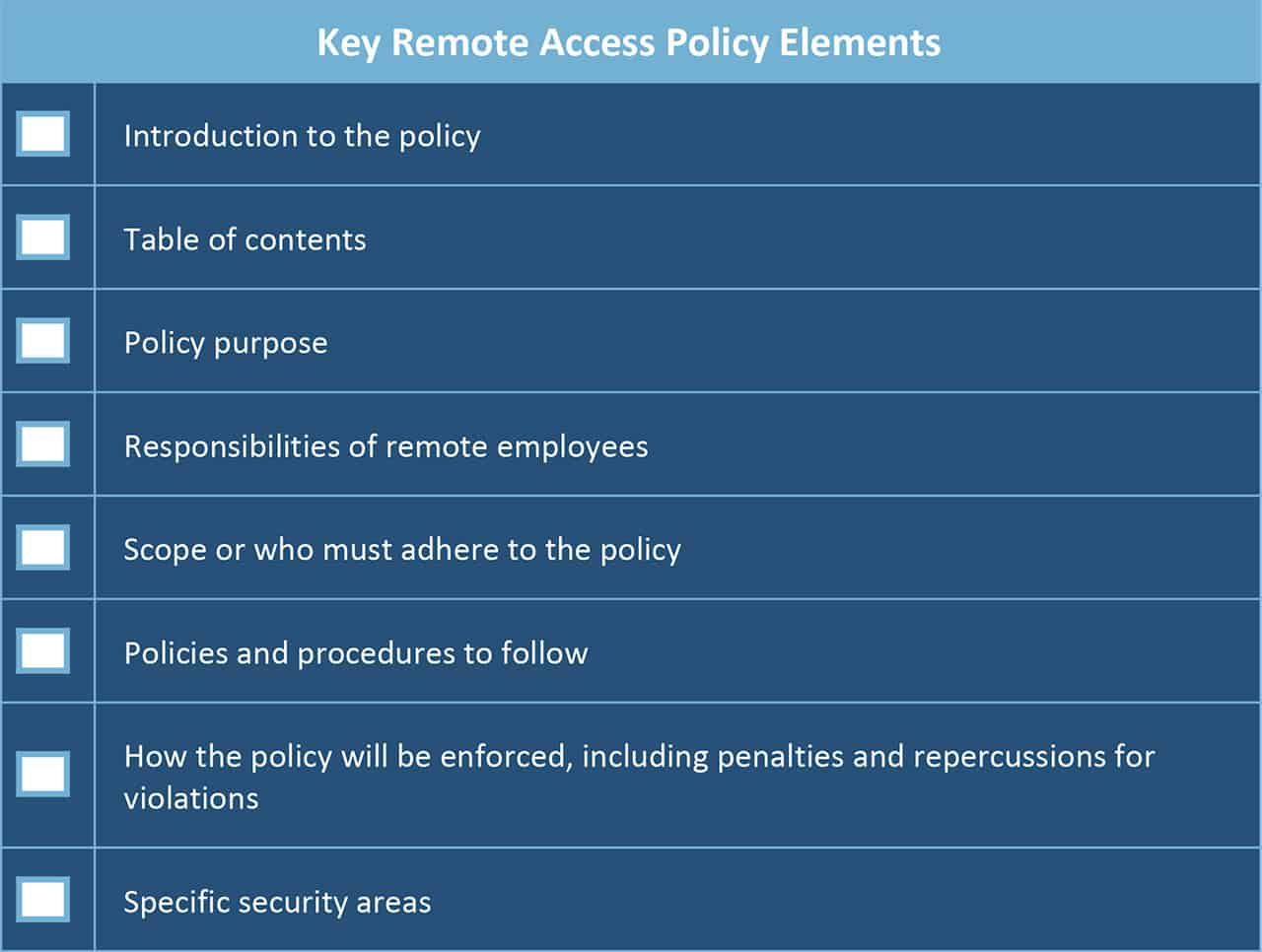
There are numerous remote access policy templates and examples available online to provide a guideline and starting point for writing a strong policy. Similar to other business policies, sections may include:
Download Key Remote Access Policy Elements Checklist
“We provide managed IT services, 24-hour support, and cloud-based everything. This requires a very stringent policy to ensure security. A few key components of our policy include:
- A truly dedicated space, a.k.a. home-office. It cannot be in a common area such as a living room or bedroom, but an actual dedicated room for true business work.
- Highly reliable Internet of at least 25Mb or greater. Since all of our phones are cloud-based, our management tools are cloud, and we need extremely fast access to our clients, so we must require high-speed Internet.
- When you are on our clock, there is no secondary activity. Yes, you may be working from home, but you are working. No babysitting anyone else, doing another job, or running errands because when our clients call, they demand and get an immediate response.”
For an idea of what to include in a remote access policy, view these examples:
- A sample remote access policy developed by the SANS Institute, an education and research organization for security professionals
- Appalachian State University’s Remote Access Policy
What Problems Arise Without a Remote Access Policy?
A strong remote access policy can mitigate a plethora of potential hazards. The policy informs off-site employees of their responsibilities in the security protocols to keep information systems secure. Therefore, consequences for misuse can also be clearly outlined to compel compliance and appropriate precautions for data use and access. Elements such as firewalls, connectivity guidelines, personal use restrictions, and antivirus updates can help IT prevent both malicious and accidental loss and disruption of corporate information assets. The remote access control policies also provide protections for confidentiality, intellectual property, and information compliance.
As we’ve discussed, remote work initiatives are on the rise throughout the world: it is called smart work in the U.K. and work shifting in Canada. Even in Japan, where people are logging more hours of on-site work than in any other industrial country, companies are trying remote options to rebuild a flagging economy, limit work related stresses, and combat a growing child care crisis. However, organizations that engage this mobile workforce need strong, enforceable policies that minimize the risks of network breaches while also providing the tools for greater productivity for remote workers. So, it’s imperative to create a remote access policy before any security breaches arise. Even if your company doesn’t currently have a demand for remote work, it’s in your interest to support it- and therefore have a standard policy in place - as work-life balance, productive and happy employees, and cost reduction will continue to drive the work-from-home trend well into the future.
Implementing Remote Access Policy in Healthcare Organizations
The ability for medical professionals and service providers to access health-related data and information from remote places is an important yet tricky policy to implement. Medical professionals must have the ability to access everything from patient status updates to X-ray images from anywhere, at anytime, all while remaining compliant with HIPAA policies and keeping protected health information (PHI) secure.
Healthcare organizations look for ways to allow remote access to critical and confidential information, yet still maintain patient privacy. To ensure that confidentiality and compliance regulations are abided by, while also supporting the technology involved in remote access, healthcare organizations need a tool to manage and track remote access and ensure all devices are equipped with stringent security software.
Smartsheet is a work execution platform that enables healthcare companies to improve data safety, manage security processes, and keep privacy in check. Securely track and share confidential information with authorized users, mange control of user access, and increase visibility into who has access to what business-critical information, while meeting or exceeding all of HIPAA’s regulatory requirements. Rest assured that your assets are encrypted and stored under strict security requirements, eliminating the threat of cyberattacks and data loss, while still enabling medical professionals to access the information they need, anytime, anywhere.
Interested in learning more about how Smartsheet can help you maximize your efforts? Discover Smartsheet for Healthcare.
Gain Visibility Into Your Remote Access Processes With Smartsheet
Empower your people to go above and beyond with a flexible platform designed to match the needs of your team — and adapt as those needs change.
The Smartsheet platform makes it easy to plan, capture, manage, and report on work from anywhere, helping your team be more effective and get more done. Report on key metrics and get real-time visibility into work as it happens with roll-up reports, dashboards, and automated workflows built to keep your team connected and informed.
When teams have clarity into the work getting done, there’s no telling how much more they can accomplish in the same amount of time. Try Smartsheet for free, today.