The Rise of the Mobile Workforce
It was not that long ago that an employee would turn off their computer, turn off their light, lock their door, and leave their work behind. When mobile phones were introduced as a productivity and convenience tool, many employers supplied Blackberry smartphones to their workforce and used the company’s platform to manage the devices. But things have changed. Now, there are multiple mobile OS platforms, new mobile devices, and numerous providers. We live in a “work from anywhere” world that often defines work not as where you go, but what you do.
All of this, along with the new regulatory rules for information security, have given rise to mobile device management (MDM). Even small and medium-sized businesses (SMBs) are adopting mobile device use at a rapid pace to increase productivity. Increasingly, employees are using their own devices – up to three products each — to get work done. But, the question remains: With so much business information now accessed on millions of mobile devices, how does a company keep critical and sensitive information secure?
What Is Mobile Device Management (MDM)?
MDM is a part of a larger set of policies and tools that encompass an entire enterprise mobile management (EMM) program. MDM deals with developing and deploying mobile device policy and controls to effectively monitor, manage, and secure the capabilities of smartphones, tablets, laptops, desktops, and other mobile devices used to conduct business (both business and employee-owned devices).
The controls provide both access and security for corporate owned content and information. MDM typically focuses on managing the entire device, while mobile application management (MAM) manages only the applications.
What Is Mobile Application Management (MAM)?
Managing the applications on mobile devices as a strategy is known as mobile application management (MAM). Often used interchangeably with MDM, MAM is the deployment, updating, and management of the relevant corporate or business applications on a device.
Mobile device management is the traditional term for the management and control of mobile devices regardless of ownership. These mobile devices are increasingly supplied by the employee and are used for both personal and business purposes. Even devices owned or supplied by organizations may be assigned permissions for personal use. To better separate the business from the personal, many businesses now opt for managing information on the devices at the application level. Application management allows for the containment and control of security and access to business information rather than control of the entire device.
The distinction between MDM and MAM is important when information is at risk, since applications can be locked out or wiped rather than the entire device. MAM platforms are growing in popularity and represent the fastest growing EMM solution. According to 451 Research, in 2016 the MAM and the platform solutions used to distribute them was a $2.94 billion industry. By 2021, the projection is over $10.2 billion.
Why Is Mobile Device Management Important?
As part of an overall process to protect sensitive and critical information, MDM has emerged to secure data even when information is accessed by devices away from the office. Information security as a critical business function is mandated by regulations under the 2002 Federal Information Security Management Act (FISMA). Even though information security is regulated, 59 percent of companies allow the use of personal devices through a BYOD (bring your own device) policy, according to Tech Pro Research. Whether at work, home, or on the road, employees will have access to company data through these devices.
MDM is an important protection for organizations because its policies keep sensitive or critical data protected regardless of whether the device is company-provided or an employee-owned. MDM provides controls for how to access information, what applications are appropriate to use on the device, and when to lock and/or wipe a device in the case of employee termination or physical loss of the product.
How Is Mobile Device Management Implemented?
Creating a strong MDM policy is the first step. This policy covers appropriate device use, approved and not approved applications (whitelists and blacklists), and security policies for Wi-Fi access and authentication. There are different ownership models that dictate use such as corporate-owned, personally-enabled (COPE) or BYOD, as well as devices that employees own but are a reimbursed expense. The MDM policy and procedures address these distinctions, all with their own rules and expectations. Policies also define accessibility and security for devices and applications.
Implementing a software solution that enables you to enforceme your policy is also critical. A business can opt for on-premises solutions with servers and in-house staff to upgrade and maintain systems. However, today, many organizations turn to software as a service (SaaS) solutions, which are easier to deploy, maintain, and upgrade.
SaaS tools are a scalable and cost-effective alternative. Devices, whether owned by the company or the employee, are registered through the tool. Then, profile is installed on the device (or in specific applications) to monitor, secure, and control the access to information. Setting up these profiles allows IT administrators to enforce the policy.
Mobile Device Management Policy
Mobile devices, whether owned by the company or the employee, open a whole new set of risks for information integrity. Even when housed on an employee-owned device, organizations are responsible for adherence to regulations. There are three enforcement areas to consider when building a policy:
Contained Personal and Business Use: This includes white and blacklisted applications, as well as training and information, and access and authentication processes.
Supported Devices and Platforms: Android, iOS, and Windows devices are commonly supported. Devices are constantly upgraded, so it’s important to ensure that there is support for various versions of an OS. Keep in mind that as additional devices (such as wearables) become staples in the business world, those products may need to be supported as well.
Compliance Policies/Rules: Include information and training for appropriate use, rules for transmitting data over the air and via Wi-Fi access, how to report a loss or breach, and when to wipe the device or remove an app.
Mobile Device Management Template
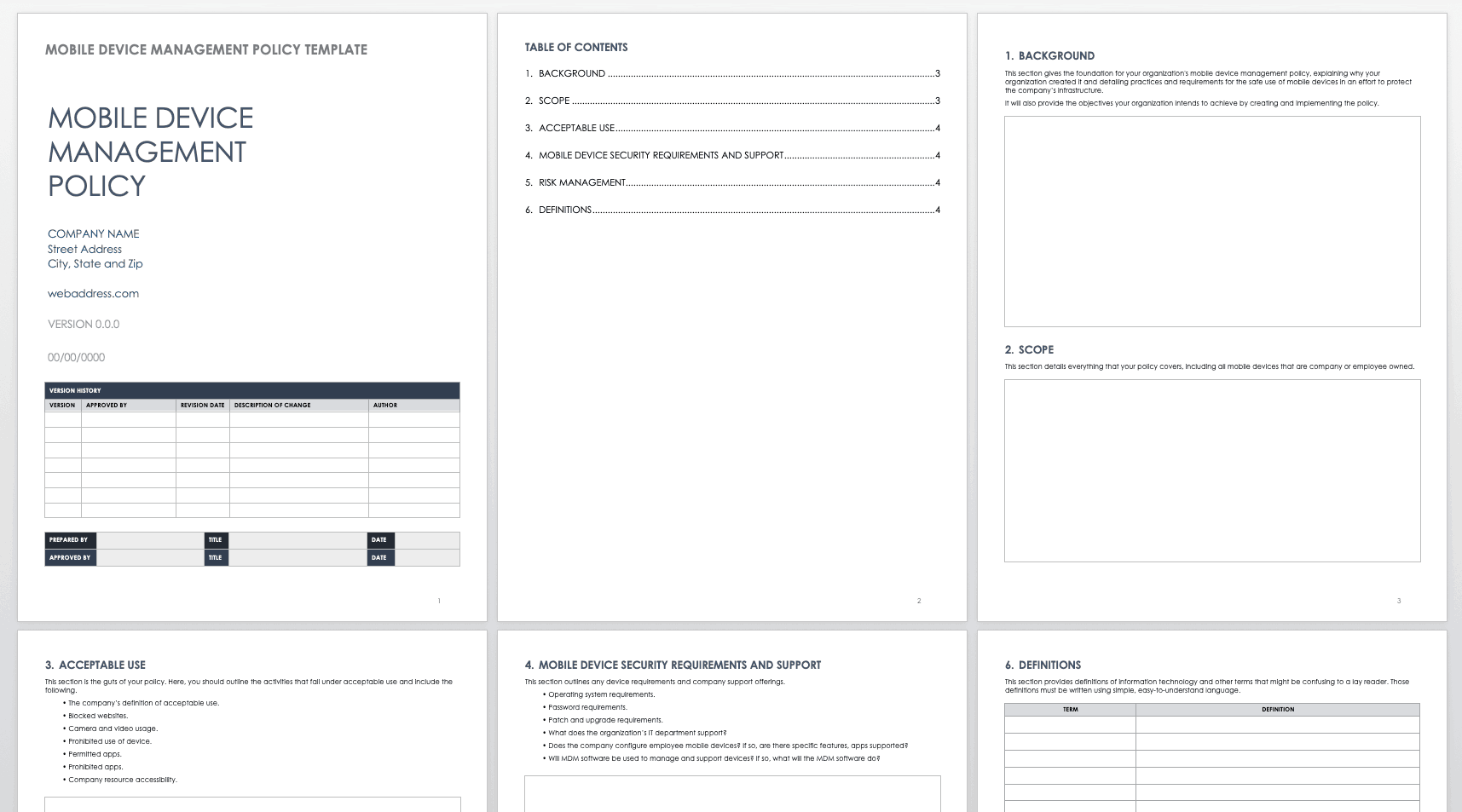
Policies also outline responsibilities of the user and the company, firewalls and security applications, and device maintenance. This template can help you get started with your mobile device management policy. It provides a framework for detailing acceptable use, supported devices, and password security, and can be customized to your organization’s needs.
Download Mobile Device Management Template
Tips and Best Practices for Implementing Mobile Device Management
Mobile device innovation is continuous, and employees often opt for the newest versions. Whether a product is provided by a company or owned by the employee, mobile access is a prerequisite for email, information retrieval, and internal business communication. To meet this demand, establish a baseline of expectations and ground rules for mobile device usage and information access.
In addition, communication, training, and education on proper use should be administered regularly. Keep staff apprised of encryption, whitelisted applications (those safe to use), as well as passwords and authentication procedures that support security.
Finally, keep in mind that devices, platforms, and applications change rapidly. Administrators should review policies on a regular basis to keep up with these changes and improvements.
Benefits of Mobile Device Management
Today, employees conduct meetings on the road, access information for presentations while having coffee at their hotel, and deliver reports from remote locations. But with increased flexibility comes inevitable security and access issues. Thorough MDM keeps a mobile workforce productive while protecting the company from the perils of information loss or breaches.
Benefits of MDM include the following:
Increased employee productivity
Increased protection against data breaches
Improved employee morale
Enhanced control of policy enforcement
Reduced equipment costs
Mobile Device Management Solutions
MDM solutions can be configured to support company-provided devices, personal devices, or any ownership combination. When looking for a mobile device management solution, there are a few basics to consider: The solution should be easy to deploy, support multiple platforms, and integrate with existing management systems. It should also provide visibility with easy-to-navigate dashboards and customizable interfaces, and have flexible cost structures. Overall, the IT department should be able to remotely control configurations, provisioning, and security of a wide range of mobile devices, including wearables.
Some of the leaders in MDM solutions include the following:
- Airwatch by VMware
- Citrix XenMobile
- Microsoft Intune
- IBM
- TeamViewer
- ManageEngine
What to Look for in an Enterprise Mobile Device Management Solution
When implementing or expanding an enterprise mobile management (EMM) policy that includes mobile information management (MIM) and mobile content management (MCM), look for an MDM solution that tracks, secures, and monitors the device. An EMM policy includes hardware and application inventory, OS configuration, remote work policies, and other information or content management functions. MDM supports the goals of EMM with 24/7 monitoring and management, and secures information accessed by mobile devices over a wide range of operating systems, including Windows, iOS, and Android. Most MDM solutions are based on a client-server model wherein the client is installed on the managed mobile devices and a server sends commands for execution. The server automatically detects devices once they connect to the network and notifies the administrator, who then deploys a client to the device.
Some of the basic capabilities that help manage and control security include the following:
Self-service and self registration functions
Data protection, including encryption, access rights, and containment
Operating system configuration and management
VPN configuration and management
Malware detection
Remote viewing, messaging, and a way to control troubleshooting/locating/tracking
Remote lock and data encryption
Automated backups and updates
Application management, including distribution, containment, monitoring, app disabling, device/app lockdown, disconnection, and wiping
Geofencing restrictions for location
Auditing, tracking, and reporting to support compliance regulations
Support for multiple operating systems
Application and device provisioning
Policy-based security, including password enforcement
Wi-Fi/Hotspot configuration
Backup/restore functions
Rooted and jailbroken device detection
As with any software solution evaluation, it’s important to consider the vendor’s architecture, delivery model (on-premise or cloud), product direction (roadmap), company reputation, and integrations.
Personal Devices
The use of personal devices in the workforce is known as bring your own device (BYOD). Personal device use at work is on the rise whether the employee works all day in the office or out on the road. Employees want to use their mobile devices to access email, send company information, quickly access/run report, and so on.
Use of personal devices comes with benefits, but those same devices pose a high risk for loss and breaches. MDM solutions can provide the necessary work and personal application separation (containment) and encrypted security to keep valuable company information safe.
Mobile device management is one part of a large puzzle that supports a “work from anywhere” environment. Enterprise mobile management is the overarching discipline that focuses on the people, processes, and technology that manage mobile computing. The availability of anywhere, anytime information has increased workforce productivity, but according to Consumer Reports, 2.1 million Americans had their phones stolen in 2014. Many of those phone have sensitive business data. Strong MDM policies and tools provide the mechanisms to not only meet the demands of the work from anywhere world, but also shield organizations from the consequences of lost or compromised information.
Glossary of Mobile Management Terms
Enterprise mobile management, along with mobile device management and mobile application management, have many supporting functions. Below is a list of important terminology.
Mobile Information Management (MIM): Provides controls and policies for information available from corporate controlled databases or public services such as DropBox, Google, or Microsoft.
Mobile Identity Management (MIM):Manages sign-on, passwords, and authentication for devices and apps.
Mobile Content Management (MCM): Manages the controls for delivering, storing, and accessing business-related content on a mobile device.
Mobile Expense Management (MEM): Provides the financial insights into mobile device usage, including costs from stipends, procurement, upgrades, and service usage.
Remote Monitoring and Management (RMM): Remote management and monitoring of client endpoint, networks, and computers.
Enterprise File Sync-and-Share (EFSS): Software that enables the secure synchronization and sharing of files. Examples include Dropbox, Box, and Google.
Random Access Memory (RAM): The hardware found within a computer or device that stores data. Device performance typically improves when there is more RAM.
Identity and Access Management (IAM): A security discipline that enables managed access to resources based on identity.
Threat Protection: The ability to screen endpoint access in order to limit threats and a possible data breach.
Open Mobile Alliance (OMA): Founded in 2002, the OMA develops standards for the mobile phone industry.
OMA Client Provisioning: A standard that allows mobile device settings and applications to be provisioned over the air (OTA).
Over-the-Air Programming (OTA): The distribution of software, settings, and updates to mobile devices or equipment.
Frequently Asked Questions About MDM
Is there additional cost for mobile management?
Mobile device management, in and of itself, does not cost anything. However, the personnel and software solutions that support mobile device management can be costly.
When an employee is terminated, is access simply shut off to the corporate systems?
Each organization is unique, but you can state what happens to a device when an employee is terminated in the mobile device management policy and execute it using the mobile device management solution.
What happens to saved or cached data on their device upon termination?
The mobile device policy will state what happens and when. However, the device may be wiped clean once an employee is terminated.
How is business data separated from a user’s personal data?
Mobile device management can apply to an entire device or be managed at the application level. Each organization will state this in their policy.
Improve Enterprise Mobile Device Management with Smartsheet for IT & Ops
Empower your people to go above and beyond with a flexible platform designed to match the needs of your team — and adapt as those needs change.
The Smartsheet platform makes it easy to plan, capture, manage, and report on work from anywhere, helping your team be more effective and get more done. Report on key metrics and get real-time visibility into work as it happens with roll-up reports, dashboards, and automated workflows built to keep your team connected and informed.
When teams have clarity into the work getting done, there’s no telling how much more they can accomplish in the same amount of time. Try Smartsheet for free, today.